Shame on You, SCO!
What's SCO up to? After publicly excoriating Linux and suing IBM, it accepted big bucks from Microsoft to license its Unix kernel. Could it be an unholy alliance designed to wipe Linux off the face of the enterprise? eWEEK's Jason Brooks has pondered the question and come to some pretty strong conclusions: SCO deserves a public flogging for twisting the truth. Our Microsoft Watch analyst, Mary Jo Foley has chimed in as well, seeing a grand anti-Linux conspiracy in the works! Follow the details of this twisted, sordid case in both analyses of the history, the present situation and what's next.
NASA Improves Computers With Tiny Carbon Tubes On Silicon Chips
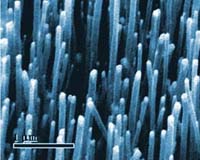
Vertically aligned carbon nanotubes about 100 nanometers in diameter. Please credit photo to NASA Ames Research Cernter. |
Moffett Field - Apr 15, 2003
The life of the silicon chip industry may last 10 or more years longer, thanks to a new manufacturing process developed by NASA scientists.
The novel method, announced in the April 14 issue of the journal Applied Physics Letters, includes use of extremely tiny carbon 'nanotubes' instead of copper conductors to interconnect parts within integrated circuits (ICs). Carbon nanotubes are measured in nanometers, much smaller than today's components
- http://www.spacedaily.com/news/chip-tech-03g.html
- Carbon nanotubes are fullerene-related structures which consist of graphene cylinders closed at either end with caps containing pentagonal rings. They were discovered in 1991 by the Japanese electron microscopist Sumio Iijima who was studying the material deposited on the cathode during the arc-evaporation synthesis of fullerenes. He found that the central core of the cathodic deposit contained a variety of closed graphitic structures including nanoparticles and nanotubes, of a type which had never previously been observed. A short time later, Thomas Ebbesen and Pulickel Ajayan, from Iijima's lab, showed how nanotubes could be produced in bulk quantities by varying the arc-evaporation conditions. This paved the way to an explosion of research into the physical and chemical properties of carbon nanotubes in laboratories all over the world.
http://www.personal.rdg.ac.uk/~scsharip/tubes.htm#history
- http://www.pcconnection.com/scripts/productdetail.asp?product_id=141259
May 22, 2003
NYC: Leverage Fiber, Offer Free Wi-Fi
By Erin Joyce
A new study from the New York City Council is recommending that the Big Apple throw open the competitive bidding process for its annual $130 million phone and Internet bill in order to leverage one of the most expansive -- and underused -- fiber optic networks in the country.
In so doing, New York City could not only cut its annual telecom bill, but would also be in a position to deploy wireless networking links as the "last mile" connecting metropolitan area networks, or MANs (define). In addition, it suggested using the fiber to deploy free Internet access with a Wi-Fi (define) Network in Brooklyn's Prospect Park.
Paris, the wireless wonder? Lee Dembart/IHT IHT Monday, May 5, 2003 In the cards: Unplugged Net surfing all over town
PARIS An experiment is under way in Paris that aims to turn the city into one huge Wi-Fi hot spot, making it what could be the first large wireless city in the world. A dozen Wi-Fi antennas have been set up outside subway stations along a major north-south bus route, providing Internet access to anyone near them who has a laptop computer or personal desk assistant equipped to receive the signals. The access is free until June 30 but will require paid subscriptions afterward. If all goes as planned, the private partners building the system expect to make a decision before the end of the year to install at least two antennas, and possibly three, outside each of Paris's 372 Metro stations and to link them through an existing fiber optics network in the subway tunnels. That would create one continuous network that would allow people to roam seamlessly throughout the city while sending and receiving data over the Internet.
Individual subscribers to the service could sit in parks, cafés or restaurants and sign on to check their e-mail or surf the Net. Businesses could create so-called virtual private networks that would let them exchange information with employees in the field or, for example, with delivery trucks. Wi-Fi, which is short for wireless fidelity, is essentially a low-power radio signal with limited range that started as a hobbyist gadget three years ago and is being ratcheted up by major companies that hope to turn it into a profitable enterprise. But no one has yet come up with a surefire plan to make that happen profitably.
The Paris project is being spearheaded by the technology consulting firm Cap Gemini Ernst Young along with two partners, Cisco Systems, which is supplying the antennas and access points, and the RATP, the agency that operates the Paris Metro, which is providing the fiber-optics link that is already in place in the subway tunnels. If the project proves successful, it could help establish Wi-Fi's viability for other large installations around the world. "We can't think of another complete city that has deployed wireless access throughout," said Ian Phillips, Cisco's manager of product marketing mobility solutions in London. Cisco is involved in several other large Wi-Fi projects around the world.
Under the best conditions, Wi-Fi signals can travel up to 100 meters (110 yards) or so, and while there are thousands of hot spots operating throughout the world, they can be finicky, and moving from one to another sometimes requires resetting things on the receiving laptop computer. Getting wireless access to the Internet requires having a Wi-Fi-equipped laptop or handheld computing device. Many new laptops come with Wi-Fi built in, and older ones can be upgraded with a card that slips into the PCMCIA slot. The cards typically cost under $100. Computer manufacturers hope that Wi-Fi will be a "killer app" that motivates consumers to buy new laptops. "We believe that giving this connectivity will develop a lot of new applications," said Jean-Paul Figer, Cap Gemini's chief technology officer. "Trucks, buses, cars, the same application has much better value if you get this kind of mobility. It's exactly like your TV remote control. It's only three meters, but it changes your life."
The Paris project opened on April 1 with antennas outside a dozen Metro stations generally following the route of Bus No. 38, which traverses Paris from north to south. It's free until June 30, and anyone can sign up at www.wixos.net. As of Sunday, 604 people had signed up. "We did not advertise, so there are relatively few people," Figer said. "The purpose of our pilot system is just to get feedback to be able to understand exactly how people will use it," Figer said, adding that adjustments would be made to accommodate users' experience and recommendations.
Based on the results of the prototype experiment, he said, he expects the partners to decide before the end of the year to go ahead with the full installation, which Figer estimated will cost E3 million ($3.4 million) to E10 million, "relatively small," he said. "It can be done extremely fast because we already have the infrastructure," he said. "Then we'll be able to offer high-speed Internet access to people in cars or buses or whatever.
Sitting at a café or restaurant or in a park you will have full access to the Internet. "We don't know how people will use it," he said. "It's the same as 10 years ago at the beginning of the Internet. The reason why we launched a huge experiment is to get the feedback of our users, to ask them how it's working, what do you need? And then we will see what kind of applications, what kind of usage will be important."
The partnership, which is called Wixos, is building the system, but the actual Internet connection will be provided by separate commercial companies, of which eight have signed up so far, six of whom have agreed to be identified: Bouygues Telecom, Club Internet, Tele2, TLC Mobile, Wifi Spot and Wifix. They will set the rates for their users; Figer said that he hoped competition among them would keep the price down. The individual operators will pay Wixos for using the system, and none of them have yet said how much they will charge users. In the United States, Wi-Fi access charges for individuals have been $10 an hour and up. "It must be much cheaper," Figer said. "The business model of trying to sell Wi-Fi to people at these huge costs will fail everywhere." "It will be interesting to see competing business models," in Paris, he said. But "we don't push a specific business model, he said. "Companies will be able to do what they want." Phillips of Cisco said that service providers will be able to provide additional premium services on top of plain vanilla Internet access. For example, he said, operators could offer businesses virtual private networks, "which give you the ability to create a secure tunnel over the public Internet into your corporate headquarters to download your corporate information." Here again, once the capability is available, no one can predict the uses that individuals and businesses will find for it. When cellular phones got going, Phillips said, "it was just voice. Then things like text messaging came along, and now we're seeing picture messaging. We're seeing data running over voice. There are different types of services that we can bundle on top of an access technology." International Herald Tribune Copyright © 2002 The International Herald Tribune
To: Winkler, Brian C [PCS]; Barcomb, John R [PCS]; Daniel Witkowski; Gregory Bahas; Gregory Heirman; Lance Watkins; Paul Barcomb; Roberta Lamanna
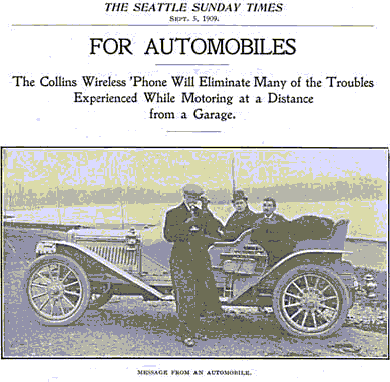
Subject: 0G Technology - Wireless Phones For Automobiles
Excerpted from:
Modern Electrics, August, 1908
The Collins Wireless Telephone
by William Dubilier, Assistant to Mr. Collins
One of the most interesting features we have been called upon to solve is an intercommunicating system of wireless telephony: The question most often asked is how a person can be called on the Collins wireless telephone and supposing there are a number of phones in use, how can you converse with any person you wish?
In the first place each wireless 'phone has a telephone number just as the ordinary 'phone, but instead of a central station and a "Hello" girl the subscriber talks direct from one station to another. This is accomplished by having three dials similar to those used on a combination safe. Each dial is numbered from 0 to 9, and the indicators of these dials are set on a number to be called up. By way of illustration, suppose Smith's number is 620, Browns number 550 and Jones' 200 ; now, when Brown wishes to call Smith he moves the indicators of his dials on his telephone to 6, to 2, and to zero, respectively. thus placing both instruments in tune with each other; he next presses a button on his telephone, which rings the bell on Smith's telephone. Smith answers, and the conversation begins just as though they were talking over an ordinary 'phone. After Brown is through talking he turns his indicators back to his own number so that Jones or Smith can call him if they so desire.
By turning the indicators to these numbers more or less inductance, capacity and resistance is thrown in or out, and as these factors determine the rate of oscillation, and the number of oscillations per second determines the wave length, it is easy to see that if a sending station have the same values as the receiving station they will be in tune.
There is no doubt as to the position wireless telephony is to occupy. Its use on the ocean will be identical to the telephone on land, while its other fields of operation are practically without limitation. Governments will use it for their army posts and ships; islands in the ocean and harbors on the continents will employ it to speak with other parts of the world; every craft that sails the ocean must adopt it, isolated mining camps, rural districts and other places will be brought into touch with the civilized world in fact, wireless telephony will enter a field entirely its own, in addition to being an aggressive competitor of the present telegraph Graph and telephone system on land.
It will enter a new, field by making it possible to telephone from automobiles to the garage when help is needed. There are thousands of automobiles in the United States, and, while touring the country in a powerful car is a delightful pastime, a breakdown several miles from. a garage or other repair shop is not conducive to pleasure. Often some member of the party finds it his lot to walk to a house for supplies, while the rest of the party, patiently or otherwise, usually the latter, await his return.
Mr. Collins proposes to eliminate this decidedly adverse feature of automobiling by employing the wireless telephone. Consequently every garage or shop will be equipped with the wireless telephone, as they are now with the tire pump and ignition plugs, and this latter day telephone will always be set up ready for use. Likewise, every auto will be provided with a portable wireless telephone. Then in the event of the inevitable accident the 'phone can be taken out, set up ready for use and communication established with the nearest garage, and an auto with men and needful mechanism sent post haste to the scene to repair it.
e-gold
http://www.e-gold.com/unsecure/qanda.html
Centrino
http://www.eweek.com/article2/0,3959,924935,00.asp
Detecting SMS fraud
http://www.observant.unimaas.nl/default.asp?page=/jrg21/obs36/art33.htm
And another wireless breakthrough, this time from Verizon --
which hopes to succeed where Metricom's Ricochet failed.
It's rolling out a 2.4Mbit CDMA 2000 network in DC and San
Diego that will compete with DSL, Cable, 1XRTT and 3G
networks. Wow!
Verizon goes wireless big time:
http://eletters1.ziffdavis.com/cgi-bin10/flo/y/eUNY0EWecc0HX60vMr0Av
VIRUS PLANTS HIDDEN BOMBS WITHIN THOUSANDS OF SYSTEMS
Over the past few weeks we've covered a range of worms that
have flooded the Internet. Although we've eradicated them,
there's chilling new evidence that these rogue programs have
infiltrated hundreds of thousands of systems. These
compromised systems are just lying in wait, ready for the
master signal that will cause them to wreak havoc across the
global Internet. It's bad, according to the CERT
Coordination center, but it's about to get a lot worse. How
bad? Read our special report on how compromised machines put
all of us at risk.
Army of PCs Ready to Attack:
http://eletters1.ziffdavis.com/cgi-bin10/flo/y/eUNY0EWecc0HX60vK70Au
Making the Most from WEP
By Steven J. Vaughan-Nichols
We all know by now that 802.11's wired equivalent privacy (WEP) isn't good enough to protect our data. That isn't just the theory, it's a fact. Sure, WEP will stop Joe Wireless, but freely available programs like AirSnort enable Joe Cracker break into your WLAN with little trouble.
Thus equipped, a cracker only needs some patience to mount a successful invasion. Specifically, it usually takes only five to ten million packets to break WEP encryption. And, at fifteen million packets, it's almost dead certain that a dedicated attacker can pry the lid off your network traffic. Or, to put it another way, a small WLAN with four active users is almost certain to be cracked with two weeks of eavesdropping.
http://www.80211-planet.com/tutorials/article.php/2106281
http://www.silicon.com/bin/bladerunner?30REQEVENT=&REQAUTH=21046&14001REQSUB=REQINT1=57064
Wednesday 15th January 2003 3:00pm
Is this the unluckiest spam recipient in Britain?
How many unwanted mails do you get? We can't help thinking it's not as many as this man...
Anybody despairing at the amount of spam they're receiving in their inbox may do well to consider the plight of one UK IT manager who has had to deal with around 500,000 unsolicited emails in just two months.
silicon.com was contacted by the IT manager of a UK firm who wished to remain anonymous ealier this week. Since November 2002, his company has been inundated with a barrage of spam, at the rate of around 8,500 emails per day.
While returning to work after Christmas was a chore for most of us, New Year was made all the worse for this IT manager - we'll call him James - by the fact that his mail server had received more than a quarter of a million unsolicited emails during the festive period - racking up 262,977 unwanted emails between 20 December 2002 and 2 January 2003.
While the problem has now been largely brought under control through the use of filtering software, James estimates that this deluge has cost him at least 10 full working days during November and December - and became so time-consuming he was even forced to turn to outside contractors to help alleviate the pressure.
Even now, constant monitoring of the filters for false-positive interceptions - where valid emails are deleted because they contain certain keywords - is an ongoing problem.
Putting an actual cost on the spam overhead is difficult, but the company's MD told silicon.com that his turnover is between £9m and £10m per year and said email is a critical tool in conducting around 90 per cent of transactions. It is easy to imagine the damage done by the two month long bandwidth-sapping spam attack.
Similarly, on top of James' own time spent dealing with the problem - and therefore being unable to touch other projects - the contractors brought in to help were paid around £600 per day.
The company has also lost all business from private customers using @msn, @hotmail, @lycos and @yahoo email addresses - as these, which were the most common senders' addresses, have now all been blocked.
James' firm, along with many others, could be being targeted by unscrupulous marketers generating random email addresses using his company's domain in the same way millions of spam emails are sent to 'all.possible.addresses@hotmail.com'.
However, there are also fears within the company that the attack may be of a malicious nature.
At the peak of the problem the sheer weight of email traffic caused a day's downtime for the Exchange server.
Mobile data to be worth $71B by 2007
According to researcher Ovum, the global market for consumer mobile data services will reach $71 billion by 2007. Traffic and subscription revenues generated by consumers using mobile data services will account for 93 percent of carriers' data revenues this year and 78 per cent by 2007. These figures do not include the value of premium content and other transaction revenues, which are supposed to further boost incomes. Currently, mobile messaging, mostly SMS, accounts for 85 percent of consumer spending on mobile data. Information and entertainment account for 10 percent and 5 percent, respectively.
By 2007, messaging will still be the primary source of mobile data revenue, accounting for about 80 percent of all usage.
For more on the study:
- see this article from Computer World
Xingtone offers software that converts MP3s for use on mobile phones
Mobile software start-up Xingtone offers a software platform that lets users convert MP3s for use on their mobile phones. Xingtone has gone live with its service, which lets people take an audio clip of a recording they own, load it through a conversion filter, and transmit it to their phone. Some recording executives have said Xingtone's service, offered without any licensing from the labels, appeared to be encouraging yet another form of digital piracy. The company said about 3,000 people have already used the service.
For more on Xingtone:
- go to the company's site
Notes towards a definition of the Web
Doc Searls and David Weinberger offer some suggestions towards a definition of the Web. Maybe these ideas will also be relevant to the mobile Internet.
- for more see their piece
Deals: Microsoft, Qualcomm strike deals in China; Toshiba, Intel ink hot spot partnerships
Microsoft talks with China Unicom; Qualcomm sets up BREW venture in China; Toshiba, Accenture roll out hot spots; Intel partners with T-Mobile, Marriott
Microsoft and Qualcomm have been striking deals in China in hopes of penetrating what promises to be the biggest growth market in this industry's history. Microsoft inked a letter of understanding with China Unicom, the country's second largest carrier, with hopes that China Unicom will adopt handsets using Microsoft's Smartphone 2002 platform.
Qualcomm formed a BREW-based venture, also with China Unicom, called Unicom-BREW Wireless Technologies. Qualcomm is aggressively pushing its BREW platform in China, a market which it hopes to convert over to the fledgling mobile content technology.
In other news, this week's deals were dominated by hot spot partnerships. First, Toshiba signed a partnership agreement with Accenture to help it roll out is new hot spot service in the U.S.
Intel is gearing up for its new Wi-Fi chip, the Centrino, by signing partnerships left and right. The company this week inked deals with T-Mobile, Marriott, the government of Singapore, and the new WISP Hotspotzz.
Also, Ericsson inked its largest Wi-Fi network deal to date with Inspired Broadcast Networks (IBN) of the U.K., agreeing to help that company install 5,000 new hot spots in that country.
Fierce wireless
March 6, 2003, 11:38PM
UT: Hackers might strike again
Officials warn fear publicity may stir more theft efforts
By ALAN BERNSTEIN and MELISSA DROSJACK
Copyright 2003 Houston Chronicle
University of Texas officials are warning that more computer hacking may be
attempted after publicity that thieves filched Social Security numbers and
other personal data on 55,200 people from a university information system.
In an internal memo, the university warned computer support staff to beware
now that the breach -- which apparently started Feb. 26 and ended Sunday --
has been made public. UT did not announce the hacking until questioned by
the Austin American-Statesman newspaper.
"The likelihood of attack and searches of the university computer systems
for other vulnerabilities rises exponentially. I ask for your immediate
attention to any vulnerabilities you may have in your systems that would
allow someone to replicate this type of attack on your information," wrote
information services director Sheila Ochner. "Think broadly in terms of ways
systems might be exploited."
Meanwhile, UT and federal officials said Thursday they were making progress
toward cornering the hackers. Also, there's a move under way in the
Legislature and among student groups to stop the use of Social Security
numbers on college and state records.
With the student assembly clamoring for change last year, UT set up a
committee to phase out the use of Social Security numbers. But it will take
years to change all of the numbers at the largest public university in the
nation, said Dan Updegrove, UT vice president for information technology.
Officials would not say whether the cyber-thieves had been identified. They
said they used search warrants to look for evidence at homes in the two
cities. Computer logs indicated the information was taken by a computer in
Austin from Feb. 26-28, and by a computer in Houston on Sunday.
UT said the exposed information included e-mail addresses, job titles and
telephone numbers for a variety of UT workers, students and former students.
No academic records or health information were obtained, the university
said.
"We thought they were protected," Updegrove said. "Protocol failed in this
case. We should have had a more rigorous system protocol."
The university apologized for not maintaining a more secure computer system
and said it will contact every person whose information was stolen.
Authorities said there was no evidence that the stolen information had been
used to set up false identities or bogus financial accounts. The data can be
used to build a profile to open credit card accounts and get access to money
and documents in other ways, say security experts.
The U.S. Secret Service said victims should wait before canceling credit
cards or closing bank accounts. Instead, they should contact the nation's
three major credit bureaus to see if their personal information was used
recently for unauthorized transactions, the agency said.
When such personal information is used fraudulently, victims should notify
police and their banks and creditors, the Texas Department of Public Safety
said.
Robert Pitman, deputy U.S. attorney for the Western District of Texas, would
not confirm or deny if there were arrests or property seizures.
"Due to prompt and efficient investigation by the United States Secret
Service and the UT Police Department, significant progress has been made in
answering these questions," Pitman said.
Lamont Rodgers, the Secret Service's special agent in charge in Houston,
would not disclose information about potential leads or results from the
execution of search warrants in Houston and Austin.
He said the hackers got a "significant amount of data." He did not indicate
how many hackers are believed to be involved.
Rodgers said agents from the Secret Service's High-tech Task Force were
working on the case with Secret Service agents in Austin. Also involved are
members of the attorney general's Internet bureau.
In a related development, the Legislature is considering bills to restrict
the use of Social Security numbers on state records.
Sen. Rodney Ellis, D-Houston, has filed a bill to protect consumers from
identity theft, and Sen. Jane Nelson, R-Flower Mound, seeks to restrict the
printing of a Social Security number on identification cards. And Rep.
Suzanna Gratia Hupp, R-Lampasas, has filed a bill to make all state higher
education institutions phase out the use of Social Security numbers as
identifiers.
Regardless, UT students, faculty and alumni listed in the violated computer
system were dealing with a giant case of identity theft.
"As students, right now in our financial situation, this could be a very
dangerous thing," UT Student Government President Katie King said. "For a
university that you trust and give your information to, the accessibility of
it is definitely in question."
Closer to Houston, Keith Weaver, former president of the Montgomery County
Texas Exes, an alumni group, said the issue was worth watching for himself
and his son, a UT student.
"I am rather concerned. I will just put it that way," said Weaver. He found
out later that his information, and his son's, were not stolen.
University computer systems frequently come under attack, according to Raj
Dhingra, vice president of marketing for California-based computer security
firm IntruVert Networks. Universities spend $50,000 to $500,000 to set up a
system that blocks intrusions, he said.
Several public institutions continue to use Social Security numbers in data
collection, said Robert Richardson, a spokesman for San Francisco-based
Computer Security Institute. He said the risks of doing so are widely known,
and that companies and organizations are gradually moving away from their
use.
From Dabbs
The Seven Rules That Weed Out Scams |
|
| |
The Seven Rules That Weed Out Scams
"When looking at telecommuting job ads, how can you tell the scams from
the real thing?"
Someone left this message on my discussion board and I thought it was an
excellent and thoughtful question. My answer is simple; there are seven
rules that can weed out the scams from the legitimate jobs. Follow these
rules and the scammers will poke out like purple roses among a field of
daisies.
First look at these examples of telecommuting advertisements:
WORK FROM HOME. Escape the rat race.
Data Entry. Earn $2,000 & up a month part-time.
Will train. Call 800-314-XXXX.
RECRUITING ASST. Responsibilities include data entry,word processing and
client/physician telephone relations. 2 years exp. in clerical field,
sales experience preferred. Work at home okay, 20 hours a week. Fax or
mail resume to: Physicians Helping, P.O. Box XXXX, L.A. CA 90026
909-382-XXXX
Now, tell me which one of these advertisements is a scam and which one
is legitimate? Don't exactly know? Well then, let's study The 7 Rules of
Legitimate Telecommuting Opportunities.
Rule 1: REAL employers ask for a resume and provide an address, an
e-mail address or/and a fax number to send that resume. Real employers
never list their phone number.
Look at the Sunday Classifieds, in the job opportunities section you
will find that most employers do not list their phone number in the
advertisement. Why? Because the employer would be inundated with calls
by the curious. Most employers do not have the time or the resources to
field all the inquiries a vacancy would produce. However, salespeople
have all the time in the world to answer calls. So, if a phone number is
listed and the ad doesn't ask for a resume, be very cautious.
Rule 2: REAL employers expect skills, knowledge and experience from
applicants and usually want proof of this via resume, samples of work or
interviews. If you are not asked for one of these things, proceed with
caution!
Rule 3: REAL employers never say "NO EXPERIENCE NECESSARY", instead they
use the term "entry-level" and most employers do not offer telecommuting
options for entry-level positions. Why? Think about it, it's difficult
enough to train the inexperienced "in" the work place. It's nearly
impossible to train someone from a distance and provide sufficient
supervision.
Rule 4: REAL employers state exactly what the job duties will be and the
skills required to fill the job. The more requirements listed; the most
likely the job is legitimate. Most scammers have absolutely no
information on job duties and requirements.
Rule 5: REAL employers usually don't list the job's salary. Now think of
the last time you saw a salary printed in a classified ad? The last one
I saw was a government job. Most employers ask for a salary history or
"salary requirement" from YOU the applicant. Also notice the amount of
salary mentioned in first advertisement. If you can make $2,000 a month
part-time (20 hours a week) you would earn $25 an hour. When have you
ever come across an entry-level position that pays $25 an hour? Do the
math!
Rule 6: REAL employers don't ask for money. They ask for your resume.
Don't EVER pay for a list of companies hiring telecommuters, because
employers are NOT looking for telecommuters, they are looking for
skilled and experience employees. Never purchase a "kit" of information,
you are looking for a job . . . not a lesson. Never pay for required
materials that you can't purchase from a third party. If you can only
purchase the materials for the employer then they're scamming you. Think
about it, most employers use materials and tools that are general to the
industry.
Rule 7: REAL employers never start their ad with phrases like WORK AT
HOME. They are not interested in finding a person "at-home"; they're
interested in finding an employee that will get the job done. Legitimate
jobs use headers that describe the open position like SECRETARY,
TECHNICAL WRITER, etc. Usually the option of telecommuting or working at
home is listed last, almost like an afterthought.
Now, you know The 7 Rules of Legitimate Telecommuting Opportunities. Go
back up to the two classified ads at the beginning of this article.
Which one is a scam? Which one does not fulfill the rules? Keep these
seven points religiously, and you will most likely field all the scams
that come your way.
-Rosalind Mays
Copyright © 2000 Rosalind Mays. All Rights Reserved.
Best-selling author of "The Real Deal on Telecommuting", and co-author
of "Get Your Money Back! Stop Scammers and Save Your Dollars"
www.telecommuting.cjb.net
Go to www.siennapublishing.com to learn more about her books. She may be
reached via e-mail at Roz-@aol.com |
http://www.topica.com/lists/OntheGo/read/message.html?mid=906144213&sort=d&start=5
The Cloud to Spread Across the UK
By Eric Griffith
George Polk, the managing director for The Cloud, a UK-wide Wi-Fi hotspot network with the potential to be the largest in Europe.
Inspired Broadcast Networks (IBN), a creator of pay-to-use digital entertainment kiosk, is the company behind The Cloud. IBN, with Leisure Link Group (LLG), runs a network of some 90,000 coin-operated "amusement terminals" at some 30,000 locations. The vast majority are analog boxes such as games or food machines, according to Polk. But new digital terminals, called Itbox, are being deployed in pubs around the UK for various forms of entertainment, including gaming, betting, or digital jukeboxes.
The Cloud's current schedule is to have 250 hotspots running by the end of April with free service to customers on a trial basis. By the end of June they plan to have 1000 commercial sites, going to 3000 by the end of the year.
The initial commercial service will be part of BT Openzone, the telecom's own hotspot service. While IBN will run the network, BT OpenZone users can roam on to it. Polk says the goal is that end-users will never even know they're not on a non-OpenZone node.
http://www.80211-planet.com/news/article.php/2106691
Microsoft muscles into business reporting 1 of 2
Front Page
Microsoft muscles into business reporting
By Martin LaMonica
Staff Writer, CNET News.com
February 13, 2003, 4:17 PM PT
Microsoft plans to embed a business-reporting feature into its SQL Server database software, a move that will likely cause jitters among specialized business-reporting software companies.
The software giant said Wednesday that in the first half of this year it will begin a testing program for SQL Server Reporting Services, a planned add-on feature for a forthcoming SQL Server database code-named Yukon. Business reporting tools pull information from databases and generate preformatted reports, such as regular updates on sales.
The company did not say when a final product would be generally available, although testing cycles for Microsoft products usually last several months or more than a year. But the announcement of the feature may make some potential customers postpone buying decisions in order to see what Microsoft has to offer, said John Hagerty, vice president of AMR Research.
"It's going to cause some consternation with some vendors--no question. But when people are buying business intelligence products, in a lot of cases they have very pressing needs," said Hagerty. Most businesses are closely tied to the providers of their existing reporting tools because they have already significant investment in that software, he added.
Hagerty pointed to two companies--Crystal Decisions and Actuate--as rivals in the business-reporting, or business intelligence, niche that might feel the most "heartburn" from Microsoft's plans. But several other companies in the category will adjust more comfortably, analysts said.
Actuate said Thursday that Microsoft's announcement does not change its product strategy, which will remain focused on large-scale reporting applications that run on multiple databases and operating systems. For its part, Crystal Decisions noted the company's long-standing partnership with Microsoft and said it will continue to extend the features of SQL Server with its own software.
With its new software, Microsoft is developing only the database server capabilities needed to generate the reports. Several companies, such as Business Objects, also sell tools to write the actual reports. Cognos, for example, is expected to announce on Monday an upgrade to Cognos Series 7 that expands on the analysis capabilities of the reporting tool and introduces a reworked Web interface.
Still, Microsoft's entry into business intelligence software does portend price pressure. Analysts expect a repeat of the effect the Redmond, Wash.-based company produced when it incorporated data analysis and data transformation capabilities into SQL Server about five years ago.
"Both analysis services and data transformation services have had a strong impact on their niche markets. For instance, both have driven down prices and brought these technical capabilities within the technical and budgetary grasp of far more companies," said Philip Russom, an analyst at Giga Information Group. "I strongly suspect that reporting services will have a similar impact on its niche market, namely server-based enterprise reporting."
Despite a general slowdown in software spending, revenue for business intelligence software continues to grow. According to research firm Gartner Dataquest, information technology buyers will spend $2 billion on business intelligence in 2003 and are forecast to spend $2.3 billion by 2005.
What Should Bill Do Next:
· http://eletters1.ziffdavis.com/cgi-bin10/flo/y/eTud0EWecc0HX60uLp0Ag
Cybersecurity Plan Relies on You: http://eletters1.ziffdavis.com/cgi-bin10/flo/y/eTud0EWecc0HX60uLt0Ak
·
· 12 layers of Adequate security:
· l Chief Security Officer
· l OCTAVE Methodology
· l Authentication
· l Firewalls
· l Intrusion detection systems
· l Virus scanners
· l Policy management software
· l Vulnerability testing
· l 3,222 vulnerabilities in 3Q of 2002
· l Encryption
· l Proper systems administration
· l Active content filtering
· l Incident Response
Plan/Business Continuity Plan
Common Sense Guide to Security for Senior Managers IS Alliance http://www.isalliance.org/news/BestPractices.pdf
lUn-patched systems create legal issues
lCulpability
lLiability
lUSA Patriot Act, Gramm-Leach-Bliley Act & SEC Reform Act 2000
lMandate Correction
lPrevent Terrorism
lProtect Financial Privacy
lPublic Disclosure to Stockholders of ALL Risk in Annual Reports
lUK Data Protection Act of 1999
lRegulatory Investigative Powers Act
lEU Data Protection standards adopted in Asia
· Federal reserve (or SEC? FSIC? ) draft white paper on business continuity and disaster recovery best guidelines are the monetary authority of Singapore
Exodus Webinar
UPI
http://news.com.com/2100-1023-963887.html?tag=fd_top
>From the Sign of the Times department... a musician is barred from selling his own music on eBay because of copyright regulations... Submitted on October 27, 2002 8:21 a.m. by StephenDownes [Refer][Research][Reflect]
http://stacks.msnbc.com/news/822693.asp
http://news.com.com/2009-1001-961291.html?tag=ni_promo_tocms
Yahoo, AT&T Wireless extend messaging
Yahoo today said that its instant messenger subscribers can now send messages to subscribers on AT&T Wireless' network -- even if they aren't Yahoo registered users. The new Yahoo service is free (ATTWS subscribers will be charged for each message they send and receive). Messaging between a PC and a handset, however, can only be initiated by a Yahoo registered user.
For more on the new Yahoo service:
- see this CNET story
PLUS: AT&T Wireless also ramped up its mobile data services today with new mobile music service. The new music service is being offered in cooperation with Warner Music Group and online retailer Amazon.com. AT&T Wireless subscribers will be able to download song clips, artists related content (like images), and tour information as well as buy CDs and ring tones through the service. The ring tones cost between 99 cents and $1.99 each.
Microsoft, RSA team on security
News.com Front Door:Enterprise
Top Page
Microsoft, RSA team on security
By Margaret Kane
Staff Writer, CNET News.com
October 8, 2002, 9:00 AM PT
Microsoft and RSA Security announced on Tuesday an alliance that will include the software giant's licensing of RSA's identity authentication software.
RSA shares were up 58 cents, or 23 percent, to $3.15 in morning trading.
Microsoft plans to integrate a component of RSA's SecurID two-factor authentication software into applications, including upgrades to its Internet Security and Acceleration Server 2000, the companies said. SecurID, which helps ensure that only authorized people gain access to a company's network or systems, requires people to identify themselves using two unique factors, such as a password and a digital certificate.
In addition, RSA has developed SecurID software for Microsoft's Pocket PC 2002 operating system for handheld computers. This means that Pocket PC-based devices themselves can authenticate a person's identity, eliminating the need for a person to use separate hardware, such as a PC or a smart card, to gain access to a network.
The SecurID software for Pocket PC is available as a free download from RSA.
Also on Tuesday, RSA announced a deal with iRevolution to create two-factor authentication so that people with mobile devices can add another layer of security when they sign into a site that uses Microsoft's Passport authentication software.
The new software will essentially let people with cell phones or other mobile devices double up on security by adding RSA's Mobile authentication software on top of Passport. The Mobile software generates one-time access codes when people log in and delivers them immediately to mobile phones, pagers, PDAs or e-mail accounts. People then enter their Passport login name and password followed by the one-time access code. iRevolution, a software services company, will act as third-party host of the combined applications and will manage additional credentials.
Top Page
Copyright © 1995-2002 CNET, Inc. All rights reserved.
Stealth P2P network hides inside Kazaa 1 of 3
News.com:Media
< Previous | Top Page | Next >
Stealth P2P network hides inside Kazaa
By John Borland
Staff Writer, CNET News.com
April 1, 2002, 5:35 p.m. PT
A California company has quietly attached its software to millions of downloads of the popular Kazaa file-trading program and plans to remotely "turn on" people's PCs, welding them into a new network of its own.
Brilliant Digital Entertainment, a California-based digital advertising technology company, has been distributing its 3D ad technology along with the Kazaa software since late last fall. But in a federal securities filing Monday, the company revealed it also has been installing more ambitious technology that could turn every computer running Kazaa into a node in a new network controlled by Brilliant Digital.
The company plans to wake up the millions of computers that have installed its software in as soon as four weeks. It plans to use the machines--with their owners' permission--to host and distribute other companies' content, such as advertising or music. Alternatively, it might borrow people's unused processing power to help with other companies' complicated computing tasks.
Brilliant Digital CEO Kevin Bermeister says computers or Internet connections won't be used without their owners' permission. But the company will nevertheless have access to millions of computers at once, almost as easily as turning on a light switch.
"Everybody will get turned on in more or less a simultaneous fashion," Bermeister said. "This will be an opt-in program...We're trying to create a secure network based on end-user relationships."
The Brilliant Digital plan is the most ambitious yet from a string of companies that have tried to make money off the millions of people who are downloading and using free file-swapping programs such as Kazaa, MusicCity's Morpheus or LimeWire.
Nearly all of the file-swapping programs now routinely come bundled with so-called adware or spyware--programs that automatically pop up advertisements while people surf the Web or that keep track of where someone surfs, information that can then be sold to marketing companies. Despite growing concerns about this bundled software, usage and downloads of the file-swapping programs are at an all-time high.
But Brilliant's plan, by tapping into the computer resources of the file-swappers themselves, has fallen into a new realm where start-ups such as Kontiki and Red Swoosh are just starting to gain traction. Those companies are trying to use peer-to-peer technology to distribute content more quickly online, but they face a battle convincing people to install their software and become distribution points.
Brilliant, by contrast, already has potentially tens of millions of computers in its network, simply by piggybacking on top of Kazaa.
According to CNET Download.com, a popular software aggregation site owned by News.com publisher CNET Networks, the Kazaa software--and by extension the Brilliant software--was downloaded more than 2.6 million times last week alone. Brilliant has been distributing the core technology for its peer-to-peer service along with Kazaa since February, Bermeister said.
The Brilliant network is based on a piece of software called "Altnet Secureinstall," which is bundled with the Kazaa software. That technology can connect to other peer-to-peer networks, ad servers or file servers independently of the Kazaa software and can be automatically updated to add new features, according to Brilliant's filing. [see the rest in Notes]
UPS sues Gator for wrongful delivery
News.com Front Door:Entertainment & Media
Top Page
UPS sues Gator for wrongful delivery
By Stefanie Olsen
Staff Writer, CNET News.com
October 2, 2002, 12:40 PM PT
Yet another company is seeking to defang Gator, the online advertising start-up whose pop-ups let businesses pitch potential customers visiting rival Web sites.
Shipping company UPS filed a lawsuit last week against Gator in the U.S. District Court of Atlanta, charging the online software provider with delivering unauthorized ads to visitors to its Web site. Gator's software, which PC users install to manage passwords, might display a Federal Express ad to people viewing UPS.com, for example.
"The problem lies in that this software causes third-party ads to pop up on our Web site, so if you visit UPS.com, an ad featuring our competitors would come up, and that's unauthorized," said UPS spokeswoman Vanessa Smith.
UPS is seeking a preliminary injunction against Redwood City, Calif.-based Gator to cease its practices. The two companies are currently in discussions.
The mammoth shipping company is the latest Web site operator to feel bitten by Gator and take action. In June, The Washington Post, The New York Times, Dow Jones News Service and seven other publishers filed a suit against Gator alleging the company's ads violate their copyrights and steal revenue. A federal judge ruled a month later that Gator must temporarily stop displaying pop-up ads over Web publishers' pages without their permission.
Gator develops software that manages passwords and form-filling for more than 10 million Web surfers who often download the application through other popular file-sharing programs. Bundled in Gator's software is a program called OfferCompanion, which monitors Web surfing behavior and delivers targeted pop-up ads to viewers. For example, a Web surfer may see an advertisement for Ford Motor--delivered by Gator--while visiting Toyota.com. Gator has been selling such advertising for more than a year and has accumulated several top-tier advertisers.
"In regards to Gator's pop-up ads, we did not authorize the use of our name and our Web site to be part of that strategy," Smith said.
Gator could not be immediately reached for comment. Gator has contended in the past that its advertisements are legal because people who download its software have given permission to the company to send them third-party promotions.
Top Page
Copyright © 1995-2002 CNET, Inc. All rights reserved.
I read your recent article on the internet about WiFi and Mesh
Networking. In case you have not picked up this, I thought that I would
to drop you a line to give you some recent news on the subject.
We have a mesh network R&D project in London called LocustWorld, which
was recently on slashdot.
http://slashdot.org/articles/02/10/01/2220255.shtml
www.locustworld.com
Locust world has all sorts of WiFi and Mesh networking materials
produced by Jon Anderson. Jon has a really strong track record in
technical invention and innovation, and we work together on a wide range
of technology projects covering SMS and other mobile technology,
internet applications, and lots of other fun stuff.
Getting on slashdot has generated a post bag of massive proportions,
which is really encouraging. The story is getting better all the time,
with thousands of people downloading the mesh networking software,
testing it in different environments, and helping to develop the
project.
If you are interested in more information drop me a line, or give me
call.
_____________________
Richard Lander
_____________________
Brand2Hand
London, UK
richard@brand2hand.com
Office: 0870 765 0950
Fax: 0870 765 0086
Mobile: 07941 183 687
_____________________
For a demonstration text
DEMO to 07816 225 290
Microsoft debuts mobile CRM
True to its word, Microsoft is making progress in the mid-market CRM space with the launch Mobile Workplace CRM, which combines sales force automation (SFA) and field force automation (FFA) tools with wireless messaging. IT analysts, however, still aren't convinced that mobile CRM is a viable market yet, even though Microsoft has signed on various A-list integration partners such as Accenture and HP. "There's an infrastructure issue," according to researcher Aberdeen. "The U.S. is building wireless infrastructure rather slowly." Pricing for Mobile Workplace CRM was not released.
For more on Microsoft's mobile CRM:
- check out this story from Line56
DoCoMo completes successful 4G test
NTT DoCoMo Inc said it completed a 100Mbps-downlink and 20Mbps-uplink wireless data experiment under an indoor environment using an experimental system for 4G mobile communications. The company has been conducting indoor trials on an experimental 4G data packet system.
· DoCoMo, the morning after
High from their success with i-mode, Japan's leading carrier NTT DoCoMo overreached in its attempt to corner the global wireless market. The company is now paying the price for its spending ways (the carrier invested over $16 billion in a group of foreign carriers, including AT&T Wireless and KPN). For a detailed analysis of the deflating of the mobile Internet's first real celebrity, see this story from Business Week.
Microsoft, RSA partner for mobile authentication
Microsoft and RSA today announced a mobile security deal that enhances the wireless version of Microsoft's Passport authentication. Microsoft has licensed RSA's SecurID two-factor authentication software, and will build a SecurID agent into the Microsoft ISA 2000 firewall product. No financial details were released. RSA, the market leader in online mobile authentication, said it plans to work more closely with Microsoft products in future, and hopes at the same time to make its Passport system more user friendly. RSA's Mobile authentication mechanism, introduced in September, sends a one-time access code to the user's mobile phone, which is used to add two-factor authentication to Microsoft's Passport authentication service.
Today's announcement is just the latest in a string from Microsoft, which is aggressively ramping up its push into the mobile market. Stay tuned for more announcements in the days to come.
For more on Microsoft's latest wireless move:
- see this story from ZDNet
http://www.hermangroup.com/coming_in_june.html
Terrell Jones chat:
What is a key differentiator of e-commerce from retail?
I think ecommerce sites have to include things that the customer cannot get in the physical world
for example on travelocity..we had a calendar based pricing system that showed people when to go to get the best fare
You simply cannot find that out from an airline!
Kinkos now has the ability to download your file, ship it to any store, print it out and deliver it
That is quite a leap from printing it out yourself, taking it to them to copy and then shipping it yourself.
If the online store isn't better than the physical world...why come?
It can't just be price...it must be something more.
Sherman Williams lets you determine how much paint you need to paint a room
Crutchfield.com will tell you what cd players will fit into your make and model of car
try that at the local electronics store...you can't get the answer
These kind of features will help draw people to your site and help you close the sale
don't think that generally more at risk, you have to look at their privacy policy And its very important for stores to have a good policy and display it
The new versions of Internet Explorer even read that policy and make sure its there before letting you shop
Travelocity has some great cruise tools where you mouse over the desk plan and your cabin photo pops up, then one click to buy
We changed behavior to the point where we were selling $15,000 cabins with a click
Barnes and noble got me away from amazon by finally giving me a discount card that works in stores and on line 30% of sears customers order on line and pick up in stores
I just did that for my daughters college computer equipment
I was able to shop quickly and pick up same day
·  http://www.tbjones.com
http://www.tbjones.com
Turning to the second point, that HIPAA will spur innovation in secure document exchange, we’re already seeing this effect. St. Paul-based VisionShare has been an innovator in health care security, having been heavily involved in the HealthKey and OpenBridge security initiatives. HealthKey is a multi-state, Robert Wood Johnson Foundation funded project that aims to create a replicable model for Public Key Infrastructure (PKI) and other secure infrastructure for the health care industry.
PKI is an encryption methodology that involves a pair of keys – a public key and a private key. If you and I wish to encrypt our communications, we each make known, or publish, our public keys, keeping our corresponding private keys secret. If I send you a message, I encrypt it using your public key, and the message can only be decrypted with your private key.
PKI methodology is a relatively well-accepted means of encrypting messages or documents. What is less prevalent is a standard means of publishing keys and a standard application to handle the encryption/decryption and communications. VisionShare’s products solve these problems with easy-to-use applications and services.
While there are a variety of solutions that provide one-to-many solutions – giving companies the ability, for example, to communicate securely with many suppliers – VisionShare aims to provide a many-to-many solution in which any health care participant and easily communicate securely with any other, without expensive or time-consuming setup. The company calls this establishing a Virtual Trusted Community.
VisionShare’s patent-pending products include the ReliaShare Secure Communications Server, which moves files from one organization to another securely over the Internet. Organizations using the server need only establish two directories on their network for each partner they wish to exchange secure documents with: one for incoming and one for outgoing documents. Usage is extremely simple: Simply drag and drop a document into the outgoing directory for the appropriate partner and the file is encrypted and automatically delivered. This works for any kind of document file, from X-rays to claims forms. The ReliaShare server also supports automated file transfers, EDI transmissions, streaming media, and remote database access.
VisionShare’s technology is currently being used on the Minnesota Health Information Network (MN-HIN). The ReliaShare Secure Communication Server encrypts and logs all traffic that passes over MN-HIN to ensure HIPAA compliance.
The company also provides the ReliaShare Secure Directory Server that can establish a central location to store and manage the components that enable secure communication over the Internet. The Secure Directory Server uses industry-standard X.509 digital certificates and certificate-enabled LDAP directory services to enable Virtual Trusted Communities for secure communications.
ReliaShare Secure Message Center (download .pdf brochure)
Cost and educational barriers can prevent the broad issuance of digital certificates to the general public. In the health care setting, however, many patients have expressed a strong desire to communicate with their health care providers and professionals via e-mail. The ReliaShare Secure Message Center provides a web-based interface to allow patients to exchange messages with doctors and other staff. Clinicians can respond to mail using their existing e-mail application.
VisionShare's approach to e-mail communication in health care is supported by a number of studies. Read the following report to learn more about the use of e-mail in health care:
Leading the Way to Health Information Exchange in the Electronic World, by Dr. Daniel Z. Sands.
The Neutralus Security Engine (download .pdf brochure)
At the heart of all ReliaShare products is the Neutralus Security Engine, a bundled Public Key Infrastructure (PKI) environment. The Neutralus Security Engine includes a full LDAP directory, directory management system and certificate management tools. It also supports unique bridging technology that allows customers to exchange secure e-mail with similarly enabled partners over the public Internet.
developed by Gartner’s Phil Redmond
accelerators behind the firewall to accelerate response of wireless apps
cybercrime.gov – rules of evidence search for federal rules of evidence – 1001
computerworld wireless newsletter – tools for detecting rogue access points in enterprise
Skip Malette, digiscout@attbi.com
Poulsbo (Kitsap County), Washington also: QUOTE OF
Despite the challenges of long loop lengths and distances from IP backbones, 65 percent of rural lines are now broadband capable, in comparison to 14 percent in 1999, according to NECA (National Carrier Exchange Association).

